
Getty Images
As Covid-19 swept the world, malware threats shot up 630%
People working from home caused hackers to shift their tactics to try and gain access to networks, according to a new report from McAfee Labs

People working from home caused hackers to shift their tactics to try and gain access to networks, according to a new report from McAfee Labs
As the coronavirus began to spread around the world, and more people started to work from home, hackers adapted too, changing the way they sought access to data and cloud-based services. Malware threats were also up, increasing 630 percent, according to McAfee Labs and its Covid-19 Threats Report for July 2020.
Calling them cybercriminals, McAfee noted that they adjusted their messages to encourage people to click on emails that included links that helped hackers gain access to databases and systems. This included phishing emails, those that seem like they're coming from a trusted source, when they're not.
These emails would include messages that tapped into fears around the pandemic to encourage people to click. "Phishing campaigns based on bogus SBA Loan emails, scam COVID-19 tests, and antibody treatments have also been detected," McAfee wrote.
Emails might be titled, "COVID-19" and "Coronavirus." And then, if someone opened the attachment or link, a form of malware would be downloaded, like the Fareit Trojan, which McAfee started to detect in February. Another, the Emotet Trojan, worked by sending spam emails from an infected account to other people's systems.
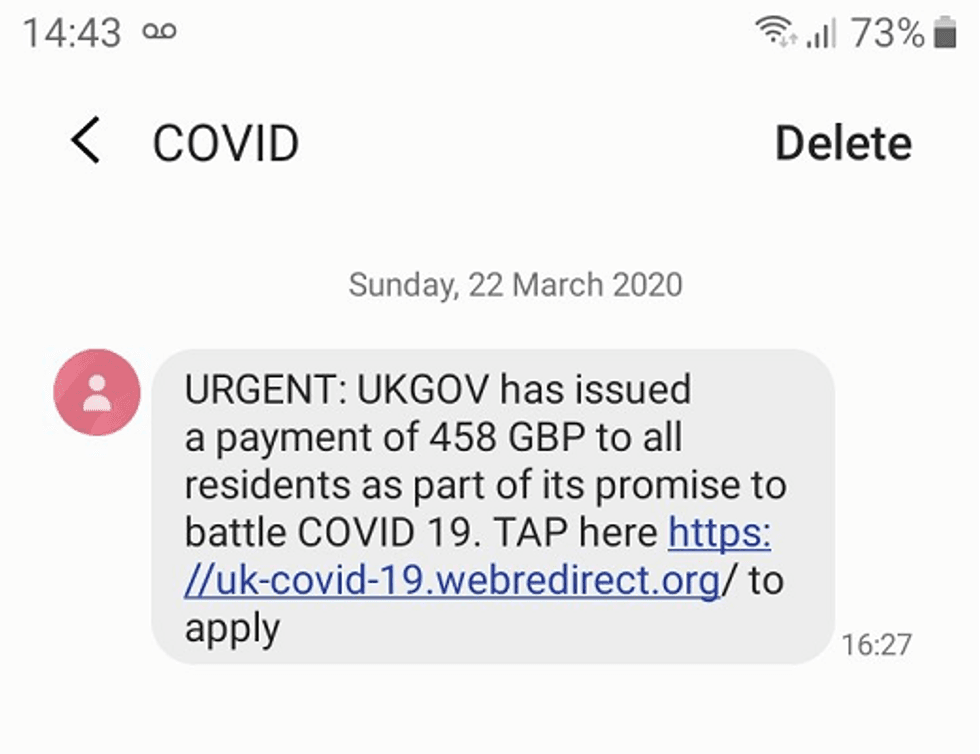
For the past several months, international security groups have been warning people about the growing prevalence of malware, specifically messaged around the coronavirus. Back in April, U.S. government groups and the Cyber Security Centre in the UK warned people that messages were being sent not just to big companies but to individuals.
Domain registrars, including Namecheap, were also noting a rise in the registrations for URLs with the words coronavirus or Covid-19 in the strings, and putting holds on these.
But some emails specifically promised not just details about fake SBA Loans, but also disguised as a coronavirus tracker, including a fake Johns Hopkins infection map, and purporting to come from other respected groups as well, like the World Health Organization, when they weren't.
The majority of the attacks focused on what McAfee calls collaboration services, programs that allow people to work together, including Microsoft 365, one in particular singled out in the report.
As the likelihood of working from home continues for the foreseeable future, McAfee encourages companies to education users about these threats — and for individuals to adopt practices that can help them avoid these traps as well.
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
