Hackers

iStock
Cybercriminals are using coronavirus fear to spread malware
Cybersecurity experts warn about new malware posing as COVID-19 information

Cybersecurity experts warn about new malware posing as COVID-19 information
Cybersecurity experts have warned internet users and smartphone owners about new and potentially dangerous malware disguised as apps and websites related to the new coronavirus.
One such Android application, called Coronavirus Tracker, was discovered by cybersecurity firm DomainTools. The app supposedly helps track cases of COVID-19, but once installed it locks the victim's smartphone and demands a $100 ransom to be paid in bitcoin within 48 hours.
Read More:
If the money is not paid, the app warns it will erase the phone's contacts, photos and videos, and publish the victim's social media accounts online.
The app, which includes the logo of Anonymous but appears to be unrelated to the hacktivist group, also states: "Your GPS is watched and your location is known, if you try anything stupid your phone will be automatically erased."
Not available through the Google Play store, where the vast majority of Android apps are safely distributed, the app is offered on a website called coronavirus[.]site, which claims to provide real-time tracking for cases of COVID-19 globally.
In reality, DomainTools senior security researcher Tarik Saleh says, "the app is poisoned with ransomware."
Saleh continues: "This Android ransomware application, previously unseen in the wild, has been titled 'CovidLock' because of the malware's capabilities and its background story. CovidLock uses techniques to deny the victim access to their phone by forcing a change in the password used to unlock the phone. This is also known as a screen-lock attack and has been seen before in Android ransomware."
Owners of Android phones running version 7.0 Nougat and later will only be affected by the malware if they do not lock their handset with a password, code, pattern or form of biometric security.
Readers are urged to never download Android apps from anywhere other than the Google Play store, and to always secure their handset.
A second coronavirus-related piece of malware to appear online this month was reported by cybersecurity expert Brian Krebs. This is web-based instead of using a smartphone app and includes a real, live coronavirus case map produced by John Hopkins University.
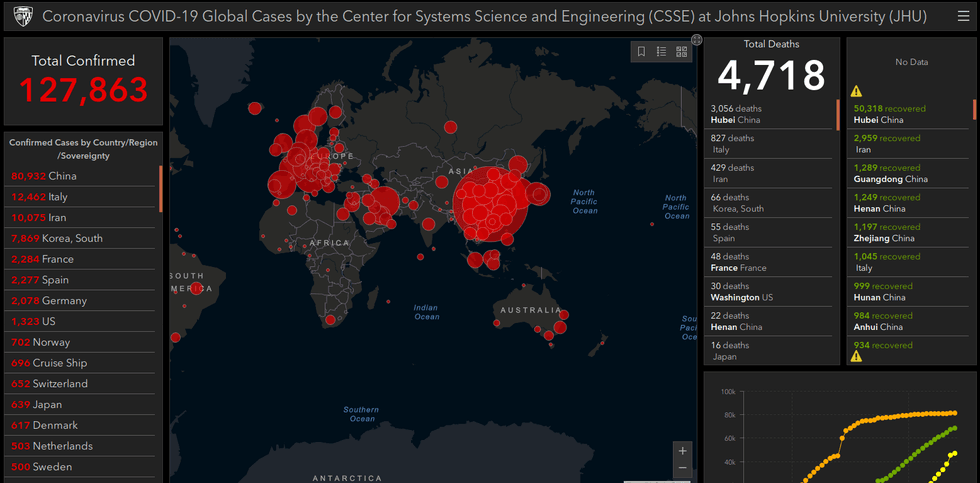
The interactive map is added to a piece of Java-based malware, which when installed on the victim's computer, via a website or email, seeks to steal their password. Krebs wrote: "Late last month, a member of several Russian language cybercrime forums began selling a digital coronavirus infection kit that uses the Hopkins interactive map".
Priced from $200, the COVID-19 malware was described by its seller as: "A fully working online map of coronavirus infected areas and other data…Map is resizeable, interactive, and has real time data from the World Health Organization and other sources. Users will think that PreLoader is actually a map, so they will open it and will spread it to their friends and it goes viral".
Both of these examples come after a report by cybersecurity firm Check Point found that, in the first two months of 2020, over 4,000 coronavirus-related website domains were registered globally.
The firm's Global Threat Index found that three percent of these websites were found to be malicious, and an additional five percent are suspicious. Check Point says coronavirus-related domains "are 50 percent more likely to be malicious than other domains registered at the same period".
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
