Hackers

iStock
Logitech flaw lets hackers control your wireless mouse and keyboard
Vulnerability also lets hackers read your private messages and passwords as you type them

Vulnerability also lets hackers read your private messages and passwords as you type them
A vulnerability in how Logitech mice and keyboards connect to their USB dongles is leaving users open to attack. Security researchers have warned that hackers could see passwords being typed and take control of the computer.
The flaw is part of Logitech's proprietary Unifying technology. This technology uses the 2.4GHz radio frequency to communicate with devices like mice, keyboards, trackballs, and presentation clickers via a small Bluetooth dongle attached to a computer's USB port.
Read More:
When hacked into, this connection can be used by a hacker to take control of the target's mouse and keyboard (while they have left a laptop unattended in a cafe or airport, for example), or even "sniff" the data going from a keyboard to the computer. This means a hacker could see your passwords and private messages as you type them.
Security researcher Marcus Mengs went public about the vulnerability last week, after Logitech said it would issue software updates to fix some but not all of the problems he found. The exploits are the same as the so-called MouseJack hack from 2016, which also affected Logitech products, and continues to do so with devices currently on sale, according to Mengs.
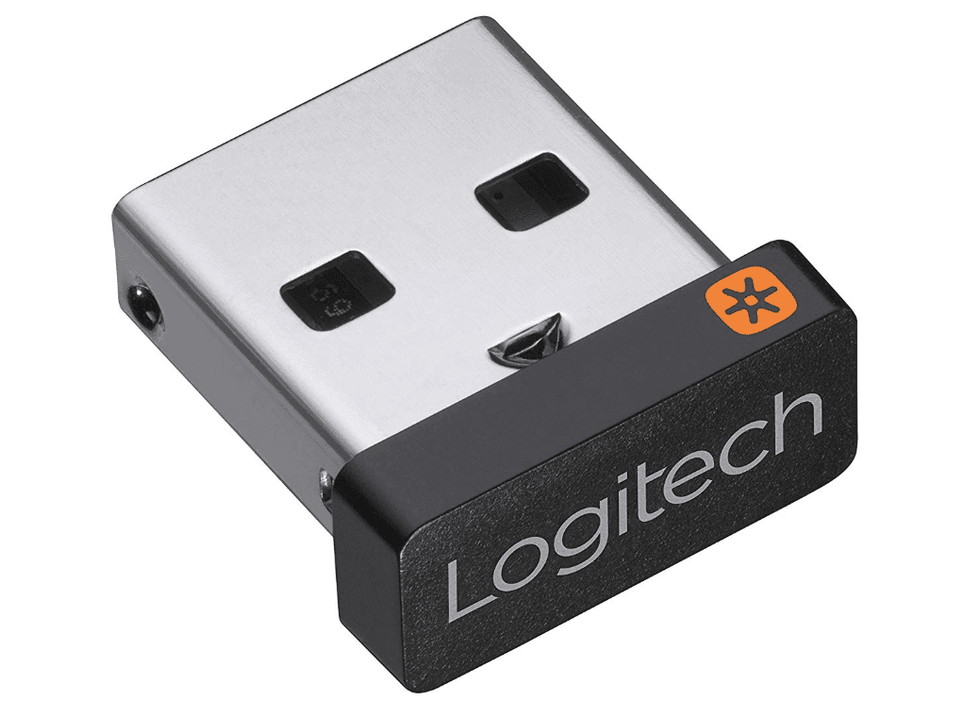
Logitech has been using the Unifying technology in wireless mice and keyboards for a decade, having introduced it back in 2009. Devices that use Unifying can be identified thanks to an orange star printed on one side of the USB dongle. These dongles are small, and often slot inside the wireless mouse for convenience when traveling.
Due to weak encryption between the device and the USB dongle, it is possible for a hacker to crack into the communication link between a keyboard and a computer during the Bluetooth pairing process. If the hacker misses this, then they can instead hack in after a moment of physical access simply by unplugging the USB dongle and plugging it back in - the work of a couple of seconds while a laptop is left unattended in a library, for example.
Mengs said of the vulnerability: "With the stolen key, the attacker is able to inject arbitrary keystrokes, as well as to eavesdrop and live decrypt keyboard input remotely...Logitech confirmed that no patch will be provided for this new vulnerability."
GearBrain TV: How to Secure your Smart Deviceswww.youtube.com
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
