Hackers
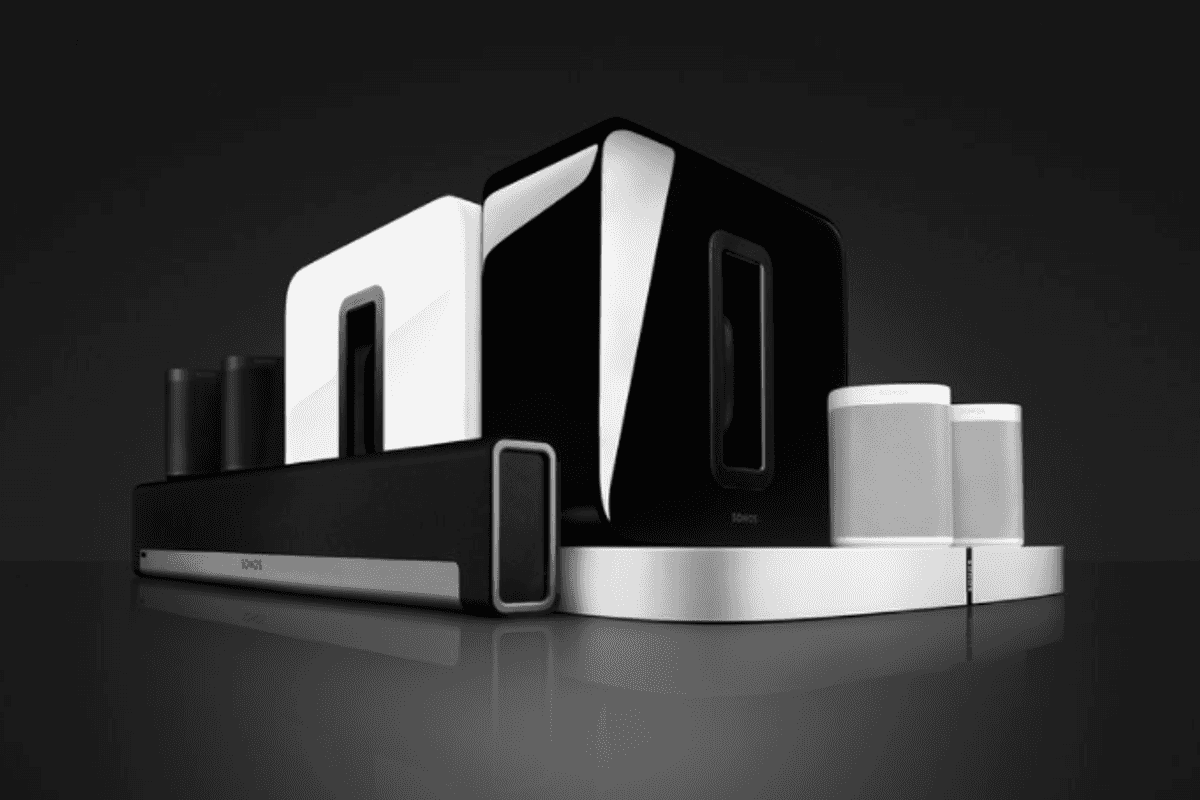
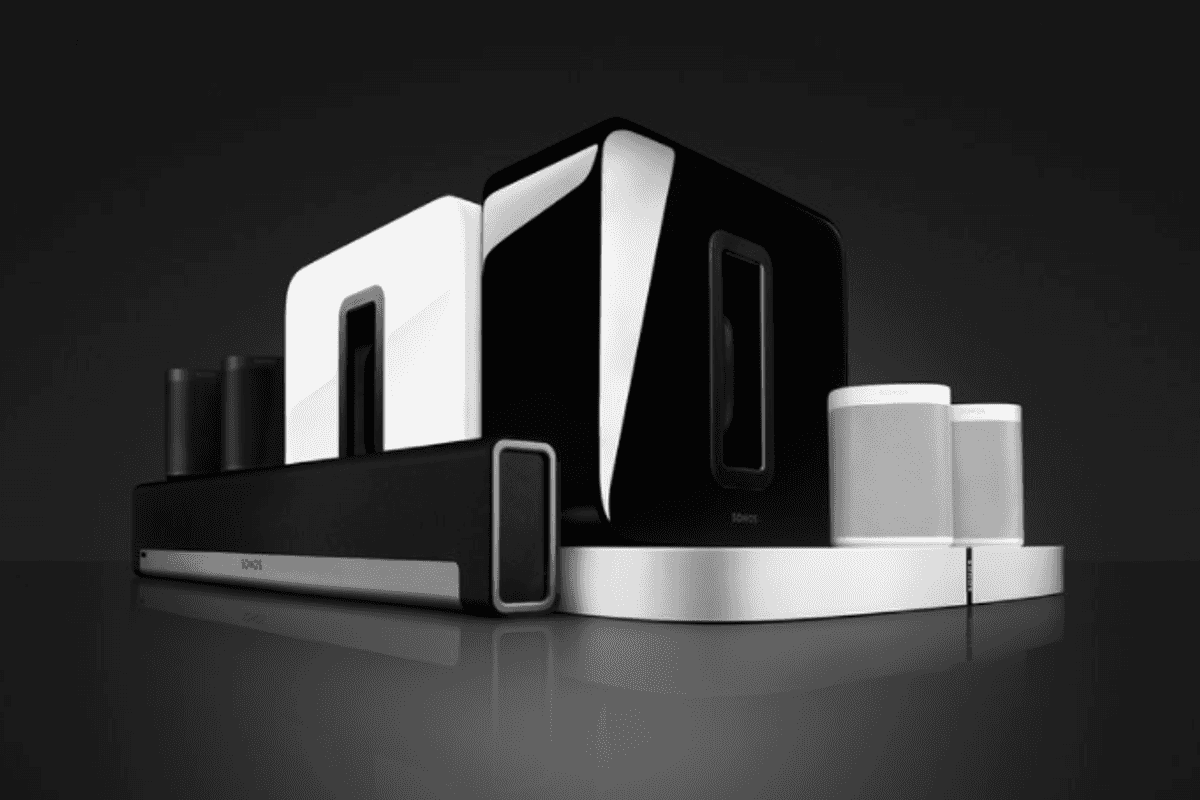
Sonos
Hackers take control of Sonos and Bose speakers to chat with Alexa and play Rick Astley
Thousands of speakers compromised by badly configured home networks
Thousands of speakers compromised by badly configured home networks
Security researchers have discovered how internet-connected speakers by Sonos and Bose can be remotely hacked and made to play any song or sound the hacker chooses.
The speakers were discovered via Shodan, a search engine for internet devicesInternet, such as cameras and speakers. Once located, the speakers could be remotely accessed and hijacked. Researchers found that the speakers could be made to play anything by directing them to the URL of an audio file hosted online. Naturally, they opted to play Rick Astley as a prank.
Taking things a step further, the hack was then used to tacontrol nearby Amazon Echo smart speaker. The researchers found hothatf the audio file they play contains the word 'Alexa',,'he compromised Sonos or Bose speaker will interact with a nearby Echo. If the victim uses Alexa to unlock doors or interact with security systems, this could help give hackers physical access to a property.
Although the Trend Micro researchers admit only a few thousand of these speakers worldwide were open to attack—due to their sitting on misconfigured and insecure networks—the threat is still real, and both smart home manufacturers and customers need to take it seriously.
The researchers say they identified between 2,000 and 5,000 Sonos devices online and vulnerable, depending on when they searched, and between 400 and 500 Bose devices. These include the Sonos Play:1, Play:3, and Play:5, plus the Sonos Playbar and new Sonos One. As for Bose devices, the company's SoundTouch systems were compromised.
The speakers can play any sound or voice command at will and reveal the name of the Wi-Fi network they are connected to and the owner's Spotify and Pandora username.
First reported by Wired, the Trend Micro research goes on to reference a post on the Sonos community forums, which claims a Sonos speaker began playing noises like a door opening, a baby crying and glass breaking at full volume. "It's started to freak me out and I don't know how to stop it," the customer wrote, before unplugging the speaker.
Mark Nunnikhoven, a research director at Trend Micro, said: "The unfortunate reality is that these devices assume the network they're sitting on is trusted, and we all should know better than that at this point. Anyone can go in and start controlling your speaker sounds".
A video published by Trend Micro says Sonos has fixed "numerous" issues relating to the vulnerability and that hacking into the speakers via this method is no longer possible.
GearBrain has reached out to Sonos for further comment, while the audio company told Wired that it is "looking into this more, but [the hack involves] a misconfiguration of a user's network that impacts a very small number of customers that may have exposed their device to a public network. We do not recommend this type of setup for our customers."
Check out The GearBrain, our smart home compatibility checker, to see the other compatible products that work with Amazon Alexa
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
