Data Protection

iStock
Google Chrome extensions spyware campaign targets 32 million users
Malicious browser extensions posed as free web security tools

Malicious browser extensions posed as free web security tools
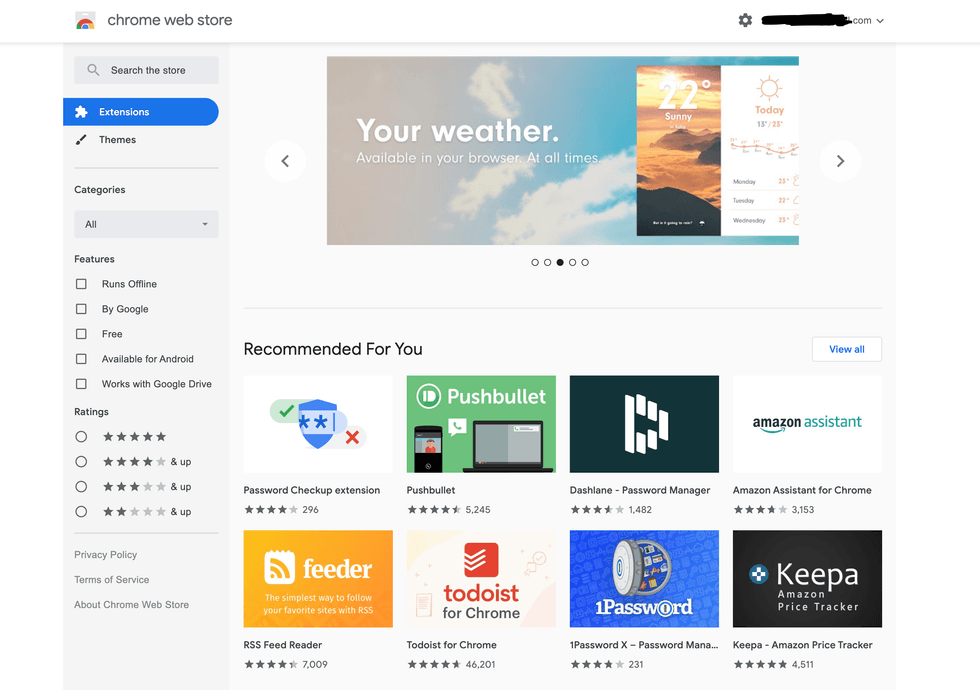
A massive spyware campaign using malicious Google Chrome web browser extensions designed to snoop on unsuspecting users has been unearthed.
One of the largest of its kind according to cybersecurity experts, the campaign saw the malicious Chrome extensions downloaded 32 million times. Although promising to warn users about suspicious websites, the extensions instead stole browser history and personal data like website login details.
Read More:
First reported by Reuters, the spyware was discovered by researchers at cybersecurity firm Awake Security, which said it was the most far-reaching Chrome store campaign to date. The malicious extensions were available for any of Chrome's two billion users to download for free from the Chrome store.
Although it isn't clear how many malicious Chrome extensions there were in total, Google says it has now removed 70 of them from the Chrome store.
A Google spokesperson said: "When we are alerted of extensions in the Web Store that violate our policies, we take action and use those incidents as training material to improve our automated and manual analysis."
Some of the extensions claimed to help flag up dubious and potentially dangerous websites to users, while others claimed to help convert files from one format to another. Instead, the browser extensions could connect the victim's computer to a series of websites and transmit personal information.
This mostly affected private individuals using personal computers, as researchers claim computers connected to a corporate network with the correct security systems in place would be unaffected by the spyware.
The extensions sent data to thousands of websites, with researchers finding more than 15,000 of them were purchased from a small domain registrar in Israel, called Galcomm.
Awake Security said it is difficult to know who was behind the spyware campaign, as the creators of the Chrome extensions provided Google with fake credentials. They were then designed to avoid detection by antivirus companies and security software.
"This shows how attackers can use extremely simple methods to hide, in this case, thousands of malicious domains," said Awake Security co-founder Gary Golomb.
Web users are reminded to remain vigilant when installing anything on their computer. Even if the Chrome store appears to be a safe place to download from, this incident shows how that isn't always the case.
Users should check the permissions demanded by every extension they install, which shows what the software plans to do, and what it needs access to. If an extension requests too many permissions, it could be best to look for an alternative. It is also good practice to regularly check what extensions you have installed, and remove the ones you no longer use.
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
