Data Protection

iStock
Why you should protect yourself online with a 2FA app, and how
Using the two-factor authentication system of a service like Facebook is not your best bet - here's the safer alternative

Using the two-factor authentication system of a service like Facebook is not your best bet - here's the safer alternative
By now, everyone should know that passwords are not a particularly safe and secure way of logging into services like social media apps, bank accounts, email and other online platforms.
They are often easy to guess, and once the hacker has your password they can quickly change it and lock you out for good. But, there is a solution, in the form of two-factor authentication.
Read More:
What is two-factor authentication?
2FA is supposed to offer an extra layer of security. This is a system which, when you log into an account — Twitter, for example — from a device the service does not recognize, like a new smartphone, a code is sent to you via text message.
You must then enter this code within a few seconds of receiving it — along with your email address and password — to gain access to the account. That way, a hacker needs access to your phone number and password to get in.
How 2FA can still be unsafe
But, while this sounds pretty secure, there are ways for hackers to hijack a target's phone number and direct the verification code to their own phone.
In some cases, all it requires is a shockingly simple piece of social engineering to steal someone's phone number — just walk into a store for the mobile network they use, then pass off their name, phone number and street address as your own. Some networks will then hand you a shiny new SIM card with the target's number on it.
So, while enabling 2FA through applications like Facebook and Twitter is one step in the right direction, it isn't the perfect solution. And, as was recently discovered with Facebook, your phone number stored as a backup contact, can end up used in ways you never knew. In Facebook's case, the company was quietly storing users phone numbers, given to the social media company for 2FA, then using this database to help new others find friends.
To bypass this, and protect your accounts from hacking via theft of your phone number, you're going to need a dedicated 2FA app. Thankfully, there are several to choose from, and they are simple and free to use.

How dedicated 2FA apps work
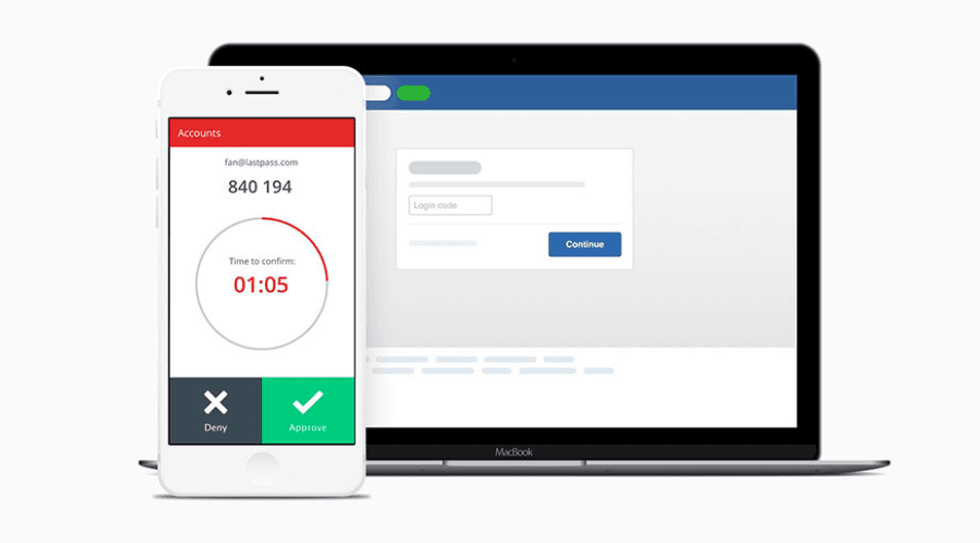
These are third-party applications which show a randomly generated six-digit code when they are opened, that refreshes every 30 seconds or so. The sequence of codes displayed is in sync with the applications you want to log into. For example, if you pair the 2FA app with Twitter, the authentication code displayed by the app will grant you access to the Twitter app, providing you enter the code within a few seconds of it being generated.
By using a 2FA app, you are protected from a hacker using your phone number, as the only way to log into the account is to have physical access to your smartphone, as well as knowing your email address and password. The hacker will also need to gain access to the 2FA app itself, which can be protected with a password, a longer pass-phrase, or with biometric security like a fingerprint or facial scan. On top of all this, your phone itself should be protected with a passcode or a form of biometric security.
While there isn't a form of digital security that is safe from being hacked, putting other stages in place will deter the vast majority of hackers.
Which 2FA app to use
A quick search of the iOS App Store or Google Play Store for '2FA app' will reveal a lot of options. Most are free, while some cost a few cents.
Two of the most popular are Google Authenticator and Authy, while password manager apps like LastPass and 1Password also include 2FA functionality.
As I already use LastPass for creating and storing all of my passwords, I'm going to use the company's own 2FA app, called LastPass Authenticator. Once I have downloaded, installed and logged into the app using my existing LastPass master password, I'm good to get started.
Unfortunately, while adding all of your accounts — like Twitter, Facebook, Gmail and others — to a 2FA app is fairly simple, it is quite a laborious, time-consuming process, and there is no way to automate it.
In short, you have to visit the service on your computer — Twitter.com, for example — then jump into the settings page and navigate to the security and login verification pages. The phrasing differs slightly between services, but most refer to adding the account to a 'mobile security app' — that's what LastPass Authenticator (or Authy, or Google Authenticator) are called.
Here, you will be shown a QR code. Now, go to your new 2FA smartphone app, tap the plus icon (in the lower-right corner of the LastPass Authenticator home page), then grant the app permission to open your smartphone's camera, which you'll then point at the QR code on your computer screen to sync everything.
A moment later, and Twitter (or whichever service you were adding) is added to your 2FA app.
After doing that, the service will be added to the 2FA app's homepage, which serves up a new six-digit code for all your services, every 30 seconds.
Authy has a good website for explaining how to add each website and online service to your 2FA app (whether you are using Authy or not).

Conclusion
There's no escaping the fact that adding all of your online services to a 2FA app takes time. But once setup, you can be safe in the knowledge that your accounts are all more secure than they were before — and you no longer have to give Facebook (or anyone else) your phone number to identify yourself.
Next time a service asks for authentication — because you are logging in from an unfamiliar device for the first time — all you have to do is open the 2FA app and hand over the code it has just generated for the service you're trying to log into.
If a hacker is trying to access your account, even if they have access to your phone number via a second SIM card setup in your name, they won't be able to get in, because they don't have access to the 2FA app.
GearBrain Compatibility Find Engine
A pioneering recommendation platform where you can research,
discover, buy, and learn how to connect and optimize smart devices.
Join our community! Ask and answer questions about smart devices and save yours in My Gear.
